



Allowing your employees to work from home is ideal for continuing the company’s day-to-day operations. However, it is also an optimal breeding ground for risks that hackers are only too happy to exploit. So what has actually changed about the risk landscape compared to working in the office? Here are five trends according to cyber experts.
Many times, VPN connections are used to log into the corporate network, or to perform work from the corporate environment. Using VPNs is highly recommended. Using a VPN connection, the data you send is encrypted and transported to the final destination. This already greatly reduces the risk of data being viewed by hackers. However, due to the huge proliferation of VPN connections, hackers focus on these very connections. In addition, not every VPN solution has a kill switch as standard. A kill switch is an option that abruptly stops all traffic over the line the moment a VPN connection is suddenly lost for whatever reason and the data travels over the line unencrypted (i.e. no encryption).
Perhaps not all your employees have experience with logging in from home. Therefore, they could potentially be easily misled. For example, it is important to know whether the remote login page for webmail ends in ‘.nl’, or in ‘.com’. Or possibly a hacker has replaced the uppercase i ‘I’ in the company name in the URL with the lowercase l ‘l’. Predictably, this can be incredibly difficult to spot, especially for employees with no experience with working remotely. It is easy for hackers to get employees to log in to a page that looks exactly like the company page, but is under the hacker’s control. After this, it is only a matter of the hacker collecting the employee’s login credentials and the hacker can log into the company network or an application with legitimate login credentials.
Given the current way of working, it is quite normal to send a file with an e-mail. Colleague B is asked to review the information in the attachment and opens the attachment. He is asked to run the macro in the file and colleague B bravely clicks yes. What colleague B does not know is that a script with malicious code is being executed in the background. Macros are great for facilitating work, but macros are also often used by hackers to send along and execute malicious code.
Where one normally walks to a colleague’s workplace, one now has to communicate through other means. Here, email is one of the first things that is used to approach a colleague. Hackers also see the increase in mail contact as an excellent source of potential spread of malicious software or access to the company network. Many employees unknowingly click on links sent by their manager or colleagues. Ranging from ‘is this interesting’ to ‘Just make sure we get something like this’. You may already be familiar with the term ‘phishing’; sending links to malicious pages or other things. Phishing and spoofing (emails in which the sender appears legitimate because the email address is almost exactly the same) are still, and especially now, effective means for hackers to gain access to personal and business data.
People currently have a huge appetite for information. Several ‘corona maps’ have now surfaced, where real-time monitoring of the situation around this pandemic can be done. There are already known of these so-called Corona cards, where the network is infected with a virus and all information stored in the browser (such as passwords and payment information) is stolen.
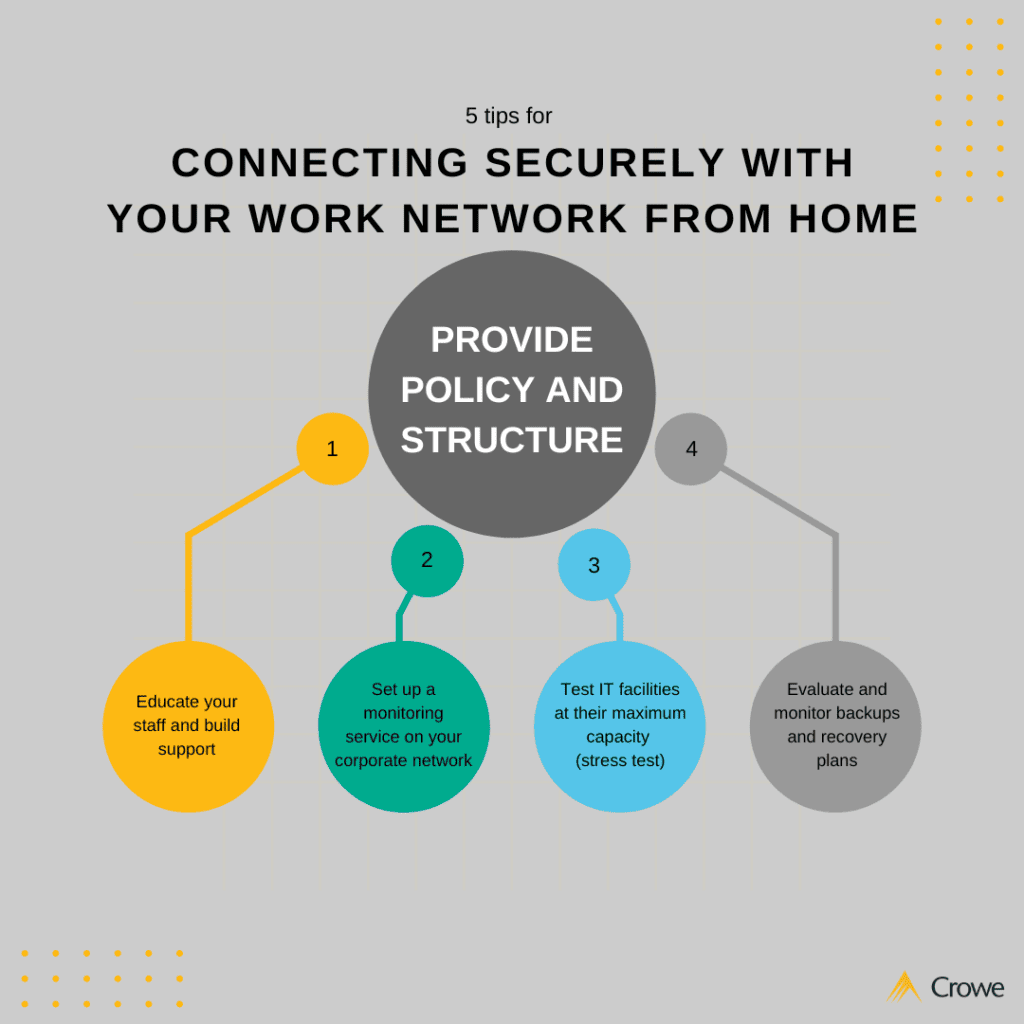
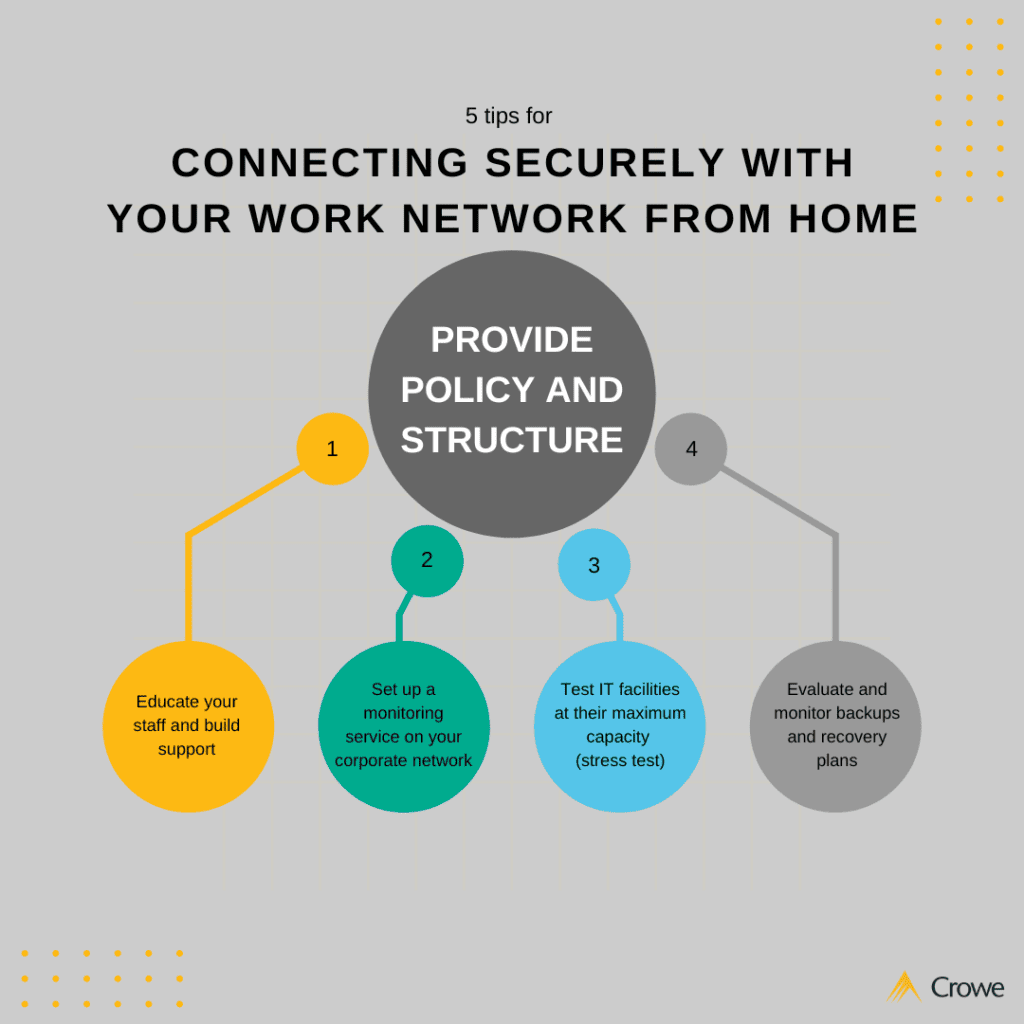
These are just some of the things that keep your IT and cyber security department awake at night. We are happy to provide some tips:
Want to know more about securing your company IT environment or testing remote login on your corporate network? Then feel free to contact our IT specialists.
Let’s meet!